Cybersecurity 101: What to Do After a Data Breach
Before you begin, remember: Don’t panic.
 Illustrations by James Pop
Illustrations by James Pop
Going about your daily routine, you get an email that reads “Your information may have been compromised in a data breach.” Now what?
With more than 10,000 security breaches reported since 2005, there are more than just email addresses and passwords at stake. Stolen info includes Social Security numbers, medical records, financial information and even fingerprints—something that you can’t change.
So let’s revisit that question: What do you do next after a security breach? Gopal Padinjaruveetil, chief information security officer for AAA, outlines the steps:
1. Confirm your data is in the breach records
If it’s a small security breach, you may get an email or text telling you your information has been affected. If it’s a major security breach, you may hear about it on the news.
“Once [companies] know there’s been a breach and it’s been confirmed, they’re supposed to let the consumers know, by law, that the data has been breached,” he says.
If you have identity theft protection, you can get immediate help confirming your data is in the breach—and determining how to move forward.
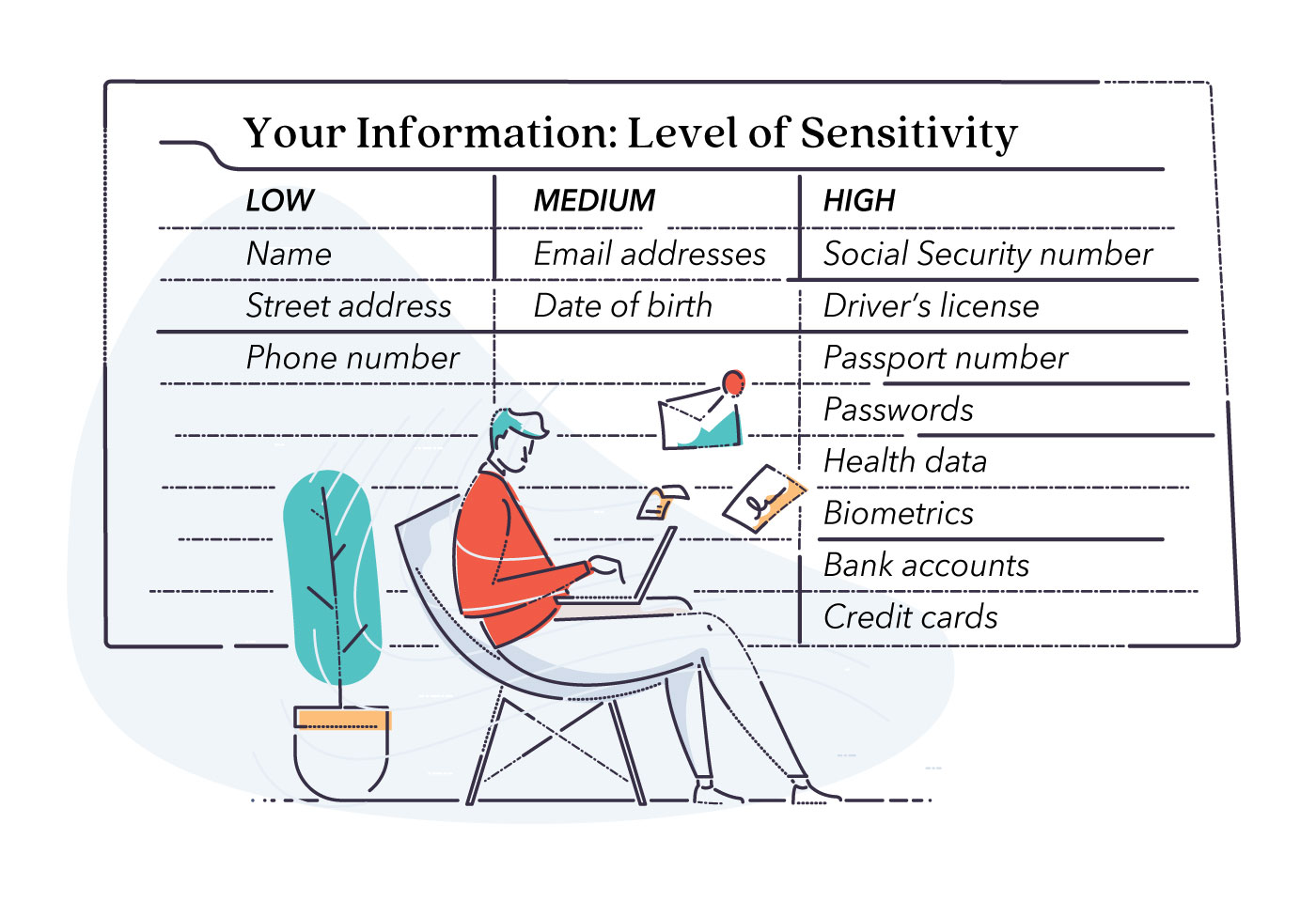
2. Find out what information was stolen
Once you’ve confirmed your data has been compromised, you need to know exactly what was stolen—because some data requires more action than others. Here’s how to tell: Think of the actions you need to take as a decision map. For example, information with a low level of sensitivity requires no further action because it’s already public information. But information with a high level of sensitivity requires immediate action because its theft can lead to serious consequences.
3. Change all affected passwords
Even if your passwords weren’t affected in the security breach, it’s worthwhile to update them anyway—especially if you had information with a medium to high level of sensitivity exposed. Use this opportunity to make your password the strongest possible and make sure it’s unrelated to the affected password.
“If I know your spouse’s or your dog’s name, I have a good chance of guessing your password,” Padinjaruveetil says. So instead of including personal information in your password, consider using a mix of letters, numbers and symbols with an uncommon phrase. And for added security, Padinjaruveetil recommends opting for multifactor authentication (providing two or more pieces of evidence that it’s really you) if any of your accounts offer it.
Once you’ve changed your password, don’t use it for everything. If you do, you may have to change all of your passwords again with the next security breach.
4. Contact relevant financial institutions
If your bank account or credit card information was compromised in a security breach, Padinjaruveetil says, the next step is to cancel the affected cards and get new ones.
Monitor your statements to see whether suspicious charges are being made to your account. If they are, work with your bank or company to dispute them. If you have identity theft protection like ProtectMyID®, the experts there can help with the fraud resolution process and tell you exactly which steps need to be taken.
5. Sign up for credit monitoring and alertsYou may have put off signing up for a credit monitoring service, but if you’ve confirmed your data is part of a security breach, the time to sign up is now. “It’s always a good idea, so if something goes wrong, you know,” he says. ProtectMyID offers more than just alerts. Available in three levels of coverage, it not only provides simple protection including credit monitoring, credit reports and fraud resolution; it can also monitor social media, the dark web, your Social Security number—even your children’s information. So if a security breach happens again or your digital identity is affected, you’ll have protection and peace of mind. |
 |
6. Consider the breached company’s offer to help
Often, affected companies offer to assist victims of the security breach—whether that’s providing the steps to take based on what information was exposed or suggesting outside resources like IdentityTheft.gov for added recovery steps.
Sometimes they may actually offer services like credit monitoring and identity theft protection. But make sure you read the fine print and understand the terms and conditions, Padinjaruveetil says.
7. Take additional action if your Social Security or passport number is stolen
Padinjaruveetil recommends these steps.
For a stolen Social Security number:
- Contact your local law enforcement.
- File a formal identity theft report at IdentityTheft.gov.
- Place a freeze on your credit.
- File your taxes early.
For a stolen passport number, contact the Department of State.